MSP Success Series: Make a List
The process of making a list (and, yes, checking it twice) yields many benefits for MSPs.
October 22, 2018

Sponsored by AT&T Cybersecurity
You’ve just closed the first sale of your MSSP service, Now what? Implementation, or, as I call it, “The Fun Part” is the next step. So, how do you know what to implement? Who’s responsible for which parts? How do I know it’s complete? The answer is a simple one: Make a list.
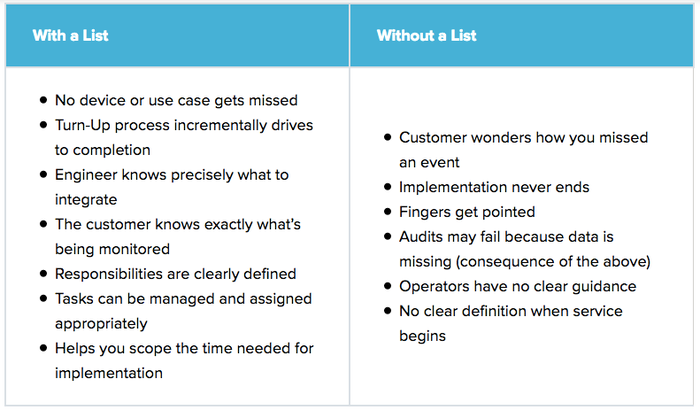
Besides the practicality of the list itself, there are many other advantages to this diligence. When you’re starting service with a customer, you’re also entering into what you hope is a long-term relationship. Setting the tone early on in this relationship is very important. If you act haphazardly or give off the impression of disorganization it could impair the relationship you need to survive. Let’s look at the scenarios with and without a list:
Gathering this information is also useful for post-implementation activities. For instance, during your event review, your in-house security analysts will already have some contextual information to use when performing their investigations. This will increase the initial fidelity of your service and bolster the customer’s perception of your service.
Lastly, this list should be something that is signed by you and the customer. This is especially important if your list includes an assignment of responsibility. The sign-off process is a mutual agreement between you and the customer, clearly stating which aspects of the turn-up you and the customer are each responsible for. This has a similar significance as your service level agreement and can be used for reference if delays are introduced.
To get you started I’ve created a sample list. Feel free to use it, but, most importantly, modify it. The services you offer and your experience will influence the creation and the ongoing edits of the document. You may also want to consider translating this information into a wiki or similar system for each customer.
Scroll to the bottom of this page for a downloadable Word document you can use to create your checklists.
You May Also Like
