Check Your Electric Bill: Malicious Cryptomining is Lighting up the Internet
Research shows there has been a 19x increase in cryptomining activity in the last nine months.
April 15, 2019

Sponsored by Cisco
For years we have been hearing about ransomware ad nauseum. Now, an emerging threat has thrust itself on the scene, and it’s taking over like wildfire: malicious cryptomining. This browser- or software-based threat enables bad actors to hijack system resources to generate cryptocurrencies for nefarious purposes.
Managed Service Providers (MSPs) and their customers should pay heed.
The market volatility of cryptocurrency typically makes this emerging threat much more financially lucrative than ransomware. Cyber thieves are drawn to cryptomining because it is an easy way for them to generate cash by attacking more people while remaining anonymous.
New findings from Cisco Umbrella research show that in the last nine months there has been a 19x increase in cryptomining activity on the internet. Umbrella protects users from connecting to malicious sites on the internet and analyzes over 175 billion DNS requests daily. The sheer volume of DNS requests gives our researchers a unique view of the internet to better identify trends on threats, enabling fast, proactive and effective protection.
Cryptomining research highlights:
There was a 19x increase in cryptomining-related traffic in the last nine months of 2018.
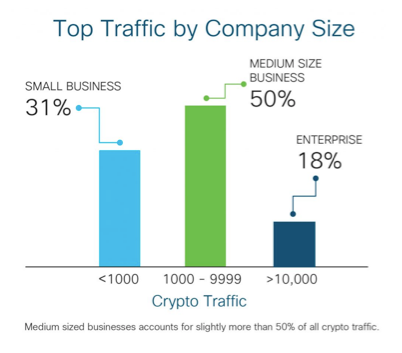
Environments with 10,000 employees or less are hit the hardest. Small businesses (1 to 999 employees) accounted for nearly one-third of all 2018 cryptomining traffic.
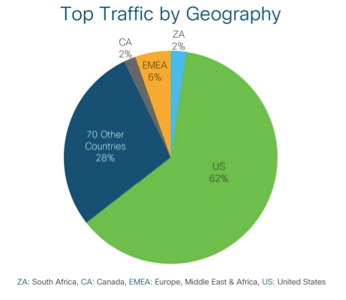
North American and European countries have heavy malicious cryptomining traffic.
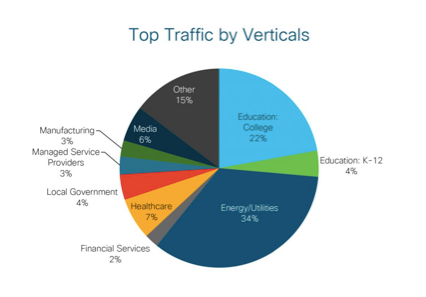
The top verticals impacted are energy, education, healthcare, local government and media. No industry is safe. Distribution of crypto traffic is spread across all industries.
Explosive Growth
In 2018, malicious cryptomining consistently ranked as one of the top threats across all internet activity. No other threat has witnessed such massive growth. Total cryptomining activity grew from approximately 600,000 queries in March 2018 to 11.3 million queries as of December 2018. That is a 19x increase in cryptomining activity across our 90 million Umbrella users.
Why Should MSPs Care?
Cryptomining in your or your customer’s environment denotes vulnerability. In and of itself, browser-based cryptomining can be concerning if it happens routinely and profusely. However, more importantly, you should always be on the lookout for bad actors installing malicious cryptomining software in your or your customers’ networks. Why? It’s simply a starting point. Attackers can leverage their presence in the network to execute future attacks. Malicious cryptomining also represents a hidden cost to your organization. Stolen computing resources impact your electricity costs, your computing costs and your bottom line.
Size Doesn’t Matter
Unwanted cryptomining is non-discriminatory. Our research shows that malicious cryptomining is highly prevalent everywhere–across all organization sizes and industries. No one is safe. All organizations need to take action to protect their resources from malicious cryptomining.
Your customers–smaller organizations that rely on you for managed IT services–are not exempt. They are also being targeted heavily. In fact, nearly one-third of all 2018 cryptomining traffic occurred in small businesses (1 to 999 employees).
Distribution of cryptomining traffic across organization sizes:
North America Is a Key Target
Traffic from our corporate users reveals that the majority of cryptomining activity is being targeted at North America. The United States accounts for 62% of the total cryptomining traffic, followed by EMEA, which accounts for 6% of the total. The remaining traffic is distributed across the globe.
Energy Industry Most at Risk
Looking at our corporate Umbrella traffic in particular, we see that about one-third of all cryptomining activity is attributed to energy and utilities organizations. Energy organizations may be hot targets due to their likeliness to use outdated systems and software that are more prone to vulnerabilities. Colleges and universities come in at second place, with 22 percent of total cryptomining activity across verticals.
Researchers say there is no sign of illicit cryptomining slowing down in the coming years. Cryptomining will continue to grow rapidly. So, why wait to get protected?
How Can Cisco Umbrella Help?
Umbrella is a cloud security platform that protects users from connecting to malicious sites on the internet. By analyzing and learning from internet activity patterns, Umbrella automatically uncovers current and emerging threats, and proactively blocks malicious requests before they reach your network or endpoints.
MSPs who use Umbrella can detect, block and protect against unwanted cryptomining in their environments by simply enabling the cryptomining security category in their policy settings.
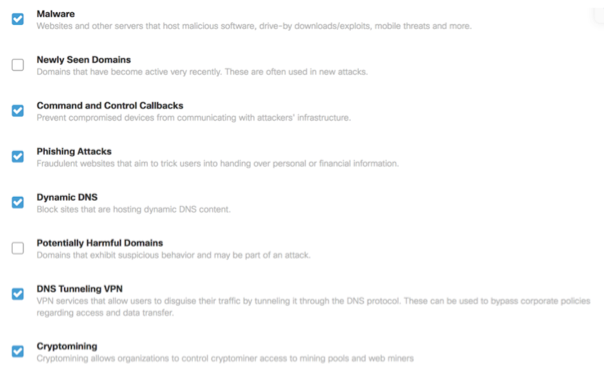
Once the cryptomining security category is selected, you can also view cryptomining activity right from the Umbrella dashboard alongside other common threat categories, such as malware, phishing, and command and control.

The ability to detect and block cryptomining is available as standard for all Umbrella customers. Here is what our customers are saying about Umbrella’s cryptomining feature:
“Cisco Umbrella helps me to report on the amount of cryptomining that I am seeing in our APAC locations.” — Richard Crowley, Chief Technology Officer (CTO), JWT
Learn more
Want to learn more about illicit cryptomining? Check out:
Cryptojacking: What’s in Your Environment?,a video presentation by our Threat Analytics Researcher, Austin McBride, and Head of Analytics and Customer Insights Ayse Firat.
Cisco Umbrella and blocking unwanted cryptomining web site.
Negisa Taymourian is a Product Marketing Manager with Cisco Umbrella. As a cybersecurity enthusiast, Negisa loves sharing with the world how Cisco security solutions can help organizations protect against attacks. Negisa’s interests include encouraging young women to pursue STEM majors and careers, leadership and organizational culture. When she is not working, Negisa loves to stay active with yoga, hiking and running. Negisa also enjoys traveling internationally and immersing herself in different cultures. Thus far, Italy is her favorite destination. Negisa holds a Bachelor of Science in Business from California Polytechnic University San Luis Obispo and a MBA from Santa Clara University.

This guest blog is part of a Channel Futures sponsorship.
Read more about:
MSPsAbout the Author(s)
You May Also Like


