While it might seem like phishing attacks have been around forever, they’ve only recently reached high levels of efficacy. No matter which anti-phishing technologies an MSP adopts, a few types of phishing attacks can still succeed.
December 21, 2016
Sponsored Content
While it might seem like phishing attacks have been around forever, they’ve only recently reached high levels of efficacy. No matter which anti-phishing technologies an MSP adopts, a few types of phishing attacks can still succeed.
Perfectly Disguised
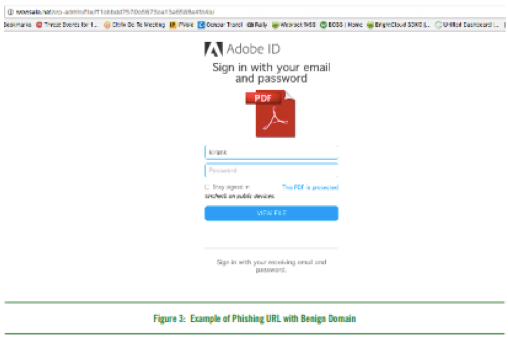
In Figure 3, we can see that hackers have even learned to disguise URLs such that they appear completely legitimate. To succeed at thwarting ever-changing phishing attacks, MSPs must adopt highly automated technologies that leverage the latest machine learning models for identifying threats. These technologies evaluate the page corresponding to each URL request and examine hundreds of characteristics of that page.
The data on the volume of new phishing sites is staggering. Throughout 2016, Webroot has monitored attempts to lure people to an average of over 400,000 phishing sites per month. To keep up with the incredibly short phishing life cycles and the sheer volume of phishing sites and URLs, old techniques that use static or crowdsourced blacklists of bad domains and URLs must be abandoned. As malware increases in speed and sophistication, static lists often become obsolete within moments of being published, if not sooner.
Top Impersonated Brands
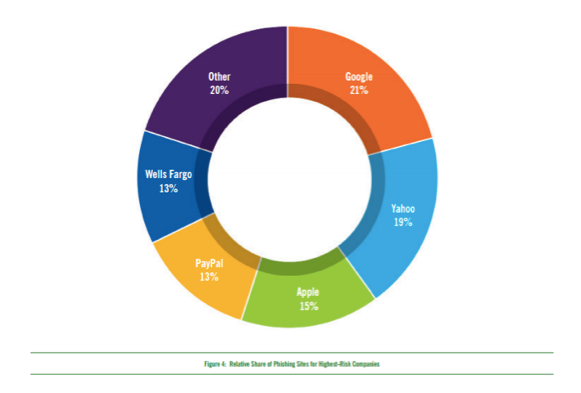
One of the most interesting trends in phishing is the specific companies that are impersonated most often. Webroot took a closer look at the companies for which impersonation would likely cause the largest negative impact: the “high-risk” companies. Of the high-risk companies being targeted, Figure 4 shows the companies with the highest number of phishing sites impersonating them between January and mid-October 2016 (Google, Yahoo, Apple, PayPal and Wells Fargo). The percentages reflect the share of phishing sites targeting the high-risk companies. For example, the chart shows that 21 percent of all phishing sites targeting high-risk companies during that time period were impersonating Google.
At first glance, the top five high-risk companies for 2016 are strikingly similar to those from 2015, which were (in order) Google, PayPal, Dropbox, Yahoo and Apple. But the relative percentages for the top impersonated targets have changed a great deal.
Figure 5 shows these changes for the four companies that appeared as top targets in both 2015 and 2016. In 2015, Google had over twice as many phishing sites impersonating it as the next highest on the list, PayPal. In 2016, Google’s relative share of the phishing sites has sharply dropped from 30 percent to 21 percent, while Yahoo’s relative share has nearly doubled, from 10 percent to 19 percent, almost matching Google’s share.
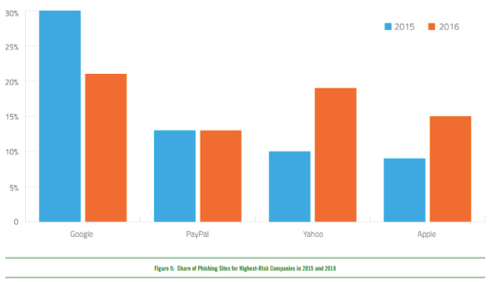
Apple’s relative share has also risen from 9 percent to 15 percent. In short, phishers are concentrating less on Google, and are impersonating a few other companies nearly as often. Taking all phishing targets into account, attackers are focusing on the same types of targets in 2016 as they did in 2015. In both years, between 55 and 60 percent of the most frequently impersonated companies were financial institutions and the rest were tech companies. Also in both years, there were far more phishing sites for tech companies than financial institutions, at approximately a two to one ratio.
Read the entire Webroot Phishing Threat Trends Report and see what else Webroot research unveiled in 2016, or check out Phishing Trends for MSPs to Watch- Part I.
Guest blogs such as this one are published monthly and are part of The VAR Guy’s annual platinum sponsorship.
You May Also Like
